Available Alerts¶
ntopng alerts are evaluated with WebUIUserScripts. Checks are executed for hosts, interfaces, SNMP devices, and other network elements, and are configurable under Checks from the Settings left sidebar.
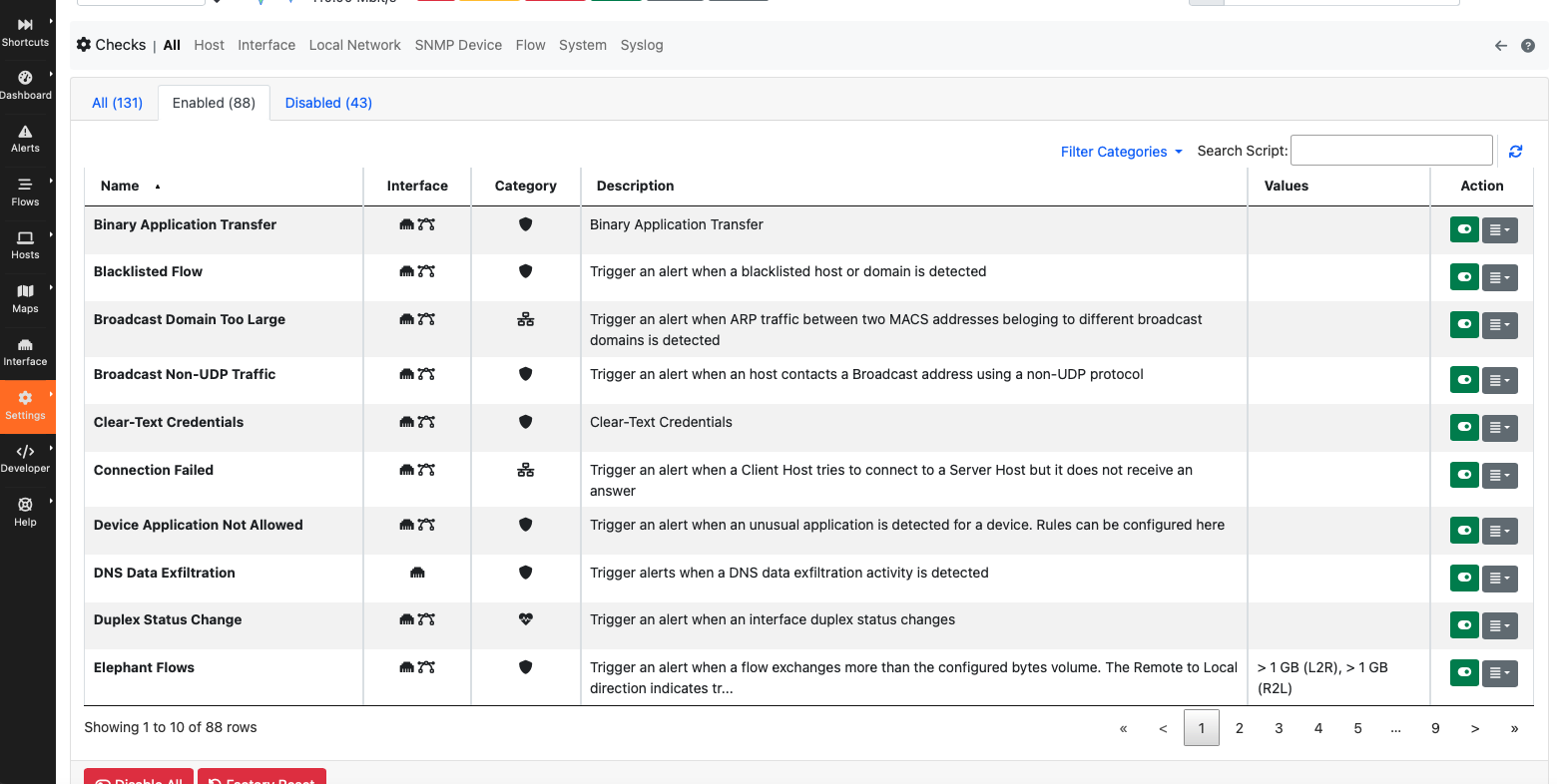
Checks are desiged to verify specific conditions and when they are not met, trigger an alert. Below you can find the list of check families and available alerts
- Host Behavioural Checks
- Countries Contacts
- Dangerous Host
- DNS Flood
- DNS Server Contacts
- DNS Traffic
- Domain Name Contacts
- Flow Flood
- Flows Anomaly
- Host External Check (REST)
- Host User Check Script
- ICMP Flood
- NTP Server Contacts
- NTP Traffic
- P2P Traffic
- Packets Exceeded
- Score Anomaly
- SYN Flood Alert
- SYN Scan Alert
- Remote Connection
- Scan Detection Alert
- Score Threshold Exceeded
- Interface Behavioural Checks
- Alerts Drops
- DHCP Storm
- Ghost Networks
- Idle Hash Table Entries
- No Traffic Activity
- Packet Drops
- Periodic Activity Not Executed
- Slow Periodic Activity
- Throughput Exceeded
- Unexpected Application Behaviour
- Unexpected ASN Behaviour
- Unexpected Device Connected/Disconnected
- Unexpected Network Behaviour
- Unexpected Score Behaviour
- Unexpected Traffic Behaviour
- Local Networks Behavioural Checks
- SNMP Behavioural Checks
- Flow Behavioural Checks
- Anonymous Subscriber
- Binary Application Transfer
- Blacklisted Country
- Blacklisted Flow
- Broadcast Non-UDP Traffic
- Clear-Text Credentials
- Crawler/Bot
- Desktop/File Sharing
- DNS Data Exfiltration
- DNS Invalid Characters
- Elephant flow
- Error Code
- External Alert
- Flow User Check Script
- Fragmented DNS Message
- HTTP Obsolete Server
- HTTP Susp Content
- HTTP Susp Header
- HTTP Susp URL
- HTTP Susp User-Agent
- HTTP/TLS/QUIC Numeric Hostname/SNI
- ICMP Data Exfiltration
- IEC Invalid Command Transition
- IEC Invalid Transition
- IEC Unexpected TypeID
- Invalid DNS Query
- Known Proto on Non-Standard Port
- Large DNS Packet (512+ bytes)
- Lateral Movement Detection
- Long Lived
- Low Goodput
- Malformed packets
- Malicious JA3 Fingerp
- Malicious JA3 SHA1 Cert
- Minor Issues
- Missing SNI TLS Extn
- ModbusTCP Invalid Transition
- ModbusTCP Too Many Exceptions
- ModbusTCP Unexpected Function Code
- Not Purged
- Obsolete SSH Client Version or Cipher
- Obsolete SSH Server Version or Cipher
- Old TLS Version
- Periodic Flow
- Periodicity Changed
- Possible Exploit
- Possible RCE
- Possible SQL Inj
- Punicody IDN
- Rare Destination
- Remote Access
- Remote to Local Insecure Protocol
- Remote to Remote Flow
- Risky ASN
- Risky Domain
- SMB insecure
- Susp DGA Domain name
- Susp Entropy
- Susp Device Protocol
- Suspicious DNS traffic
- TCP connection Issues
- TCP connection refused
- TCP No Data Exchanged
- TCP Packets Issues
- TCP With No Answer
- TCP Zero Window
- TLS (probably) Not Carrying HTTPS
- TLS Cert About To Expire
- TLS Cert Expired
- TLS Cert Validity Too Long
- TLS Cert Issues
- TLS Cert Self-Signed
- TLS Fatal Alert
- TLS Susp ESNI Usage
- TLS Suspicious Extension
- TLS Uncommon ALPN
- TLS Unsafe Ciphers
- Unexpected DHCP
- Unexpected DNS
- Unexpected NTP
- Unexpected SMTP
- Unidirectional Flow
- Unsafe protocol
- VLAN Bidirectional Flow
- WEb Mining
- XSS Attack
- System Behavioural Checks
- Syslog Behavioural Checks
- Local Traffic Volume Rules