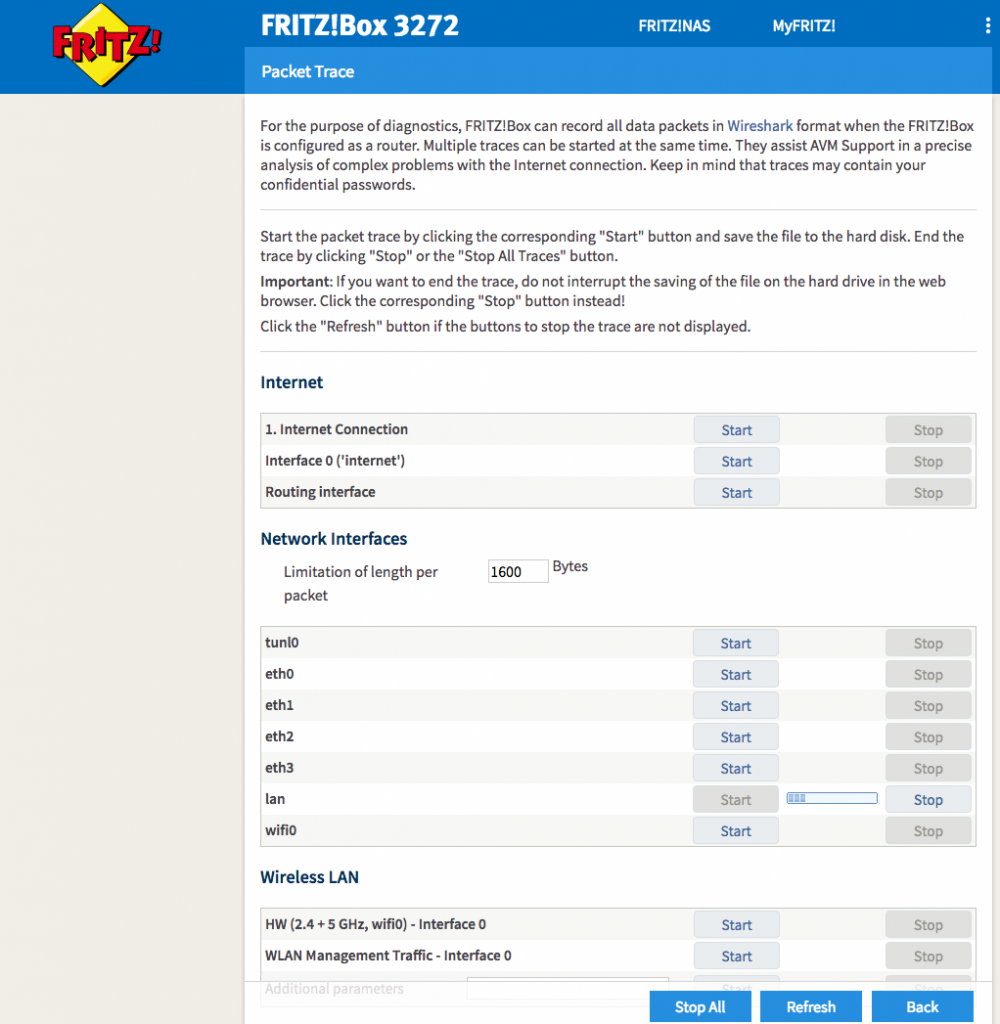
Fritz!Box routers are popular devices that many people use to connect to the Internet. Inside these routers there is a hidden (i.e. not accessible from the router web admin page, but that you access directly with a web browser by writing the whole URL) URL http://192.168.2.1/html/capture.html (BTW replace the 192.168.2.1 IP address with your Fritz!Box router IP if you have changed it) that can be used to dump router traffic in pcap format.
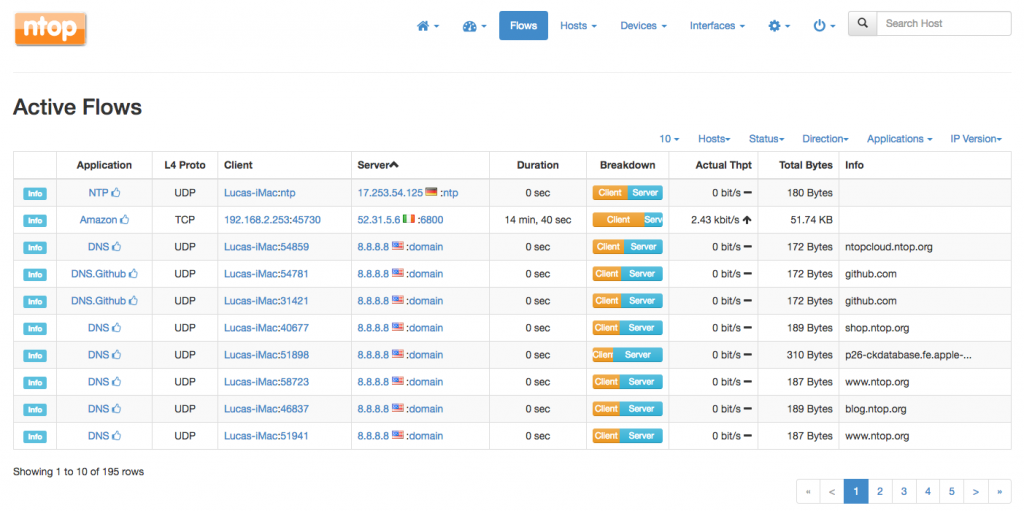
While pcaps are good for troubleshooting, most people need to know what is happening on their network in realtime, so they can spot for instance bandwidth hogs or high-latency communications. In essence we need to tell ntopng to analyse traffic flowing in our router. This is exactly what the fritzdump.sh script is doing: connect to your Fritz!Box router, start the packet capture process and spawn ntopng for analyzing the network traffic by reading traffic from a pipe (see the picture below).
This is a great solution for home and small business users that can monitor the network traffic in realtime without having to deploy network probes, taps etc. that are not affordable (in terms of complexity but sometimes also from the price standpoint) on most small networks.
Enjoy!