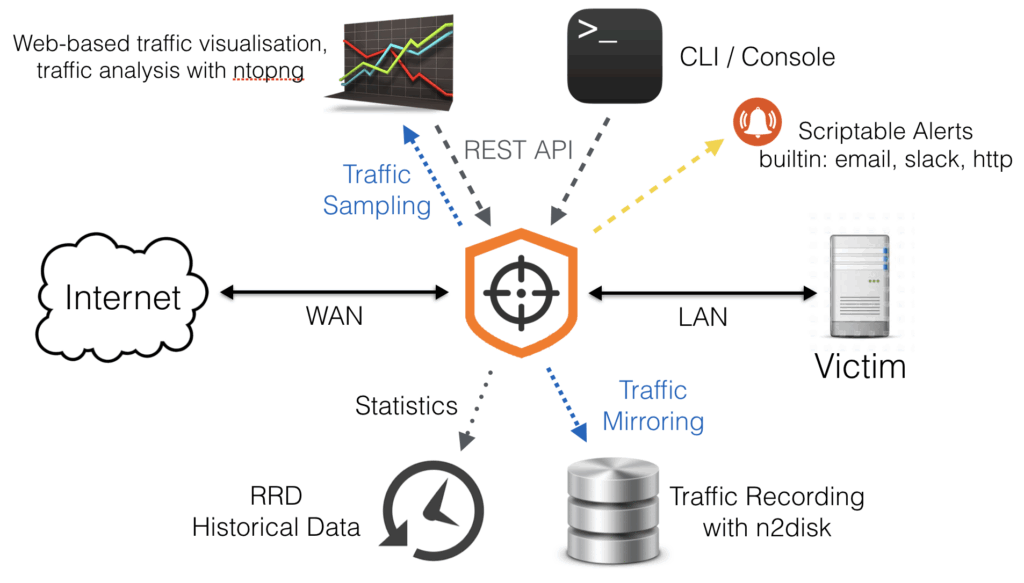
nScrub is a DDoS mitigation system based on PF_RING ZC, able to operate at 10+ Gbps line-rate using a low-end system, and scale to Terabit/s building a modular architecture.
nScrub can be implemented as bump in the wire (transparent bridge) or as router (to be used with BGP diversion techniques), both in asymmetric mode (i.e. mitigate only one traffic direction, from Internet to the protected network) or symmetric mode (i.e. mitigate from Internet to the protected network, but also forward the outbound traffic).
nScrub has been designed as an extensible platform, meaning that it can be extended for the definition of new additional algorithms for traffic mitigation, to be used in addition to those part of nScrub.
nScrub provides a REST API for configuring the engine, combined with a shell-like CLI tool with auto-completion.
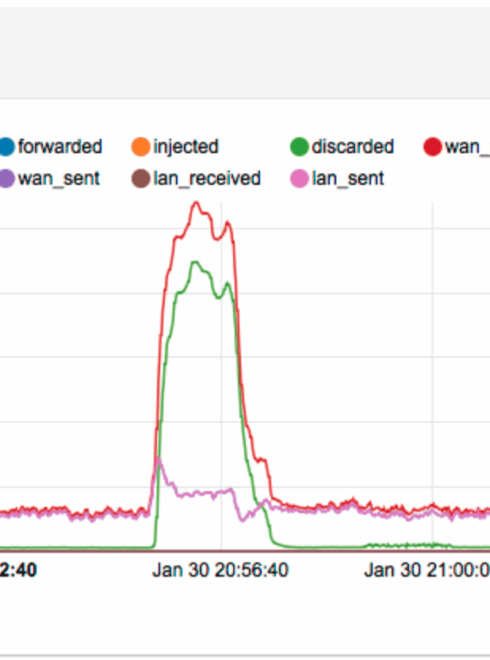
A Web-based RRD-style historical graphs, combined with PCAP dump on request triggered by an event-driven scriptable engine, guarantee full visibility on DDoS attacks. nScrub is able to export sampled/full good/bad/all traffic to external virtual devices for analysis.
at a glance
Key Features
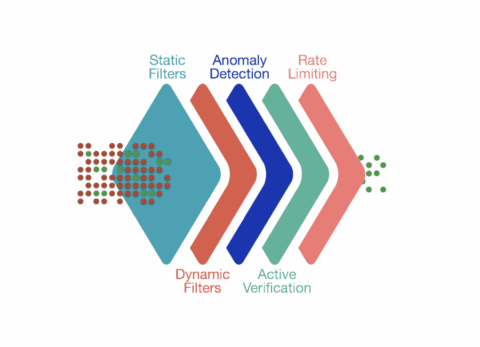
- Multi-layer traffic enforcement
- Active sessions verification for protocols including TCP and DNS
- Flexible subnet blacklists and whitelists
- DNS check, force DNS over TCP
- ACL-like policies based on UDP/TCP/ICMP fields
- Signature-based filtering, HTTP requests filtering
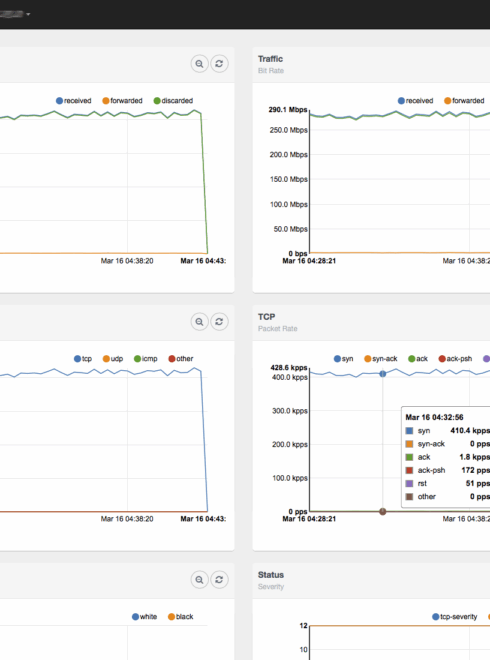
- Anomaly detection based on traffic behavior
- Rate limiting based on source, destination, protocol
- Plugins support to load custom checks and validate additional protocols
- Multi-tenancy support with configuration of multiple mitigation profiles by destination
- Web-based UI with historical graphs and statistics
- PCAP dump on request triggered by an event-driven scriptable engine
Ideal for Every Environment
Use Cases
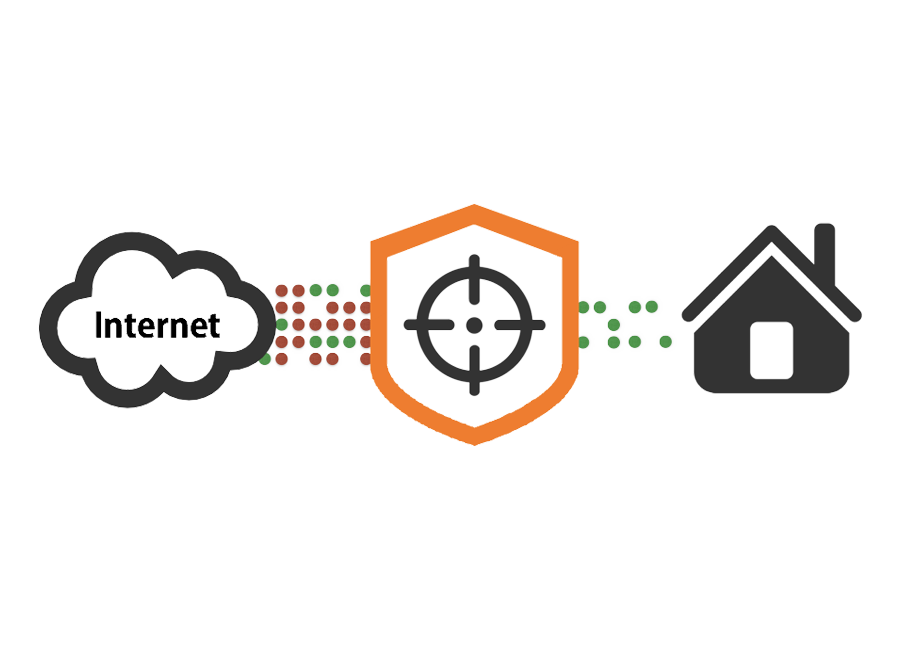
On-Demand Traffic Diversion and Mitigation
When operating in routing mode, nScrub offers the ability to dynamically divert and mitigate traffic on demand during a DDoS attack. Rather than permanently rerouting all traffic through the mitigation infrastructure, nScrub allows selective steering of suspicious or attack-bound flows only when necessary. BGP is a common option used to implement this. This targeted approach ensures minimal latency impact during normal operations, while providing rapid, efficient protection when under threat. By integrating seamlessly into existing network topologies, nScrub in routing mode enables flexible, on-demand traffic diversion, keeping your services online and your mitigation costs under control.

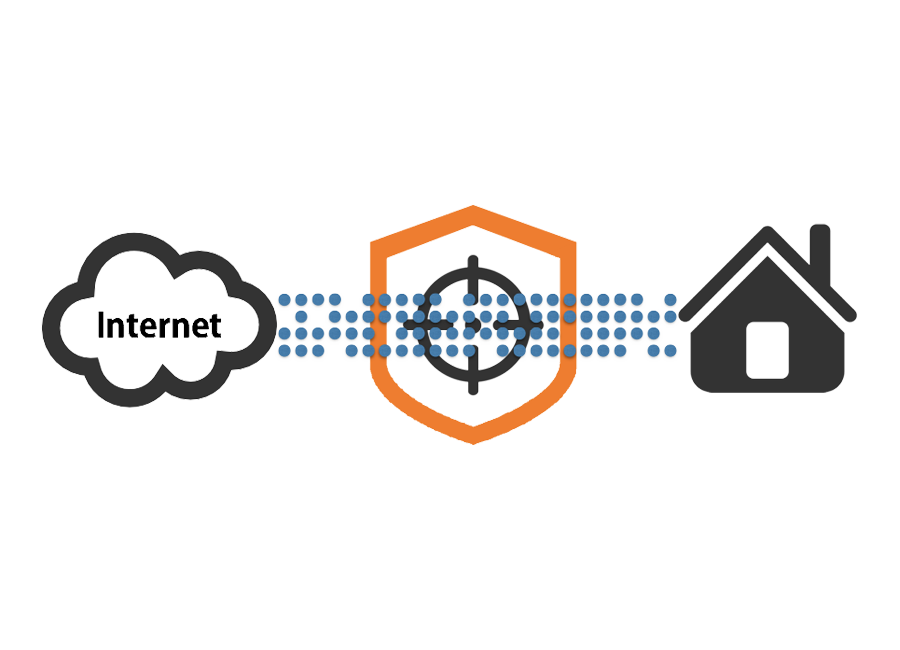
Auto Mitigation Engage with Transparent Bridge
Running nScrub in transparent bridge (Bump-In-The-Wire) mode offers seamless, zero-configuration DDoS protection. Deployed inline, nScrub forwards all traffic untouched under normal conditions, with no need for traffic diversion or routing changes. When an attack is detected, mitigation is automatically engaged, filtering malicious traffic in real time while allowing legitimate flows to pass through uninterrupted. This mode provides always-on protection with minimal operational complexity, making it ideal for environments where simplicity and reliability are critical.
Always-On Reliable Mitigation with Hardware Bypass
In environments where uptime is paramount nScrub can be deployed in transparent bridge mode combined with hardware bypass for maximum reliability and zero disruption. In this setup, nScrub operates inline as a bump-in-the-wire device, inspecting and forwarding traffic without modification under normal conditions. When a DDoS attack is detected, mitigation is instantly and automatically engaged, blocking malicious traffic in real time. If the system experiences a power failure or software crash, the hardware bypass ensures uninterrupted traffic flow, allowing packets to continue passing through without delay or loss. This configuration offers the following key advantages:
- No configuration required: plug-and-play setup with no need for routing changes or traffic diversion
- Always-on protection: automatic mitigation only when needed
- Fail-safe operation: hardware bypass guarantees network continuity, even in failure scenarios.
With this approach, organizations can achieve robust, transparent DDoS defense with the highest levels of operational reliability.
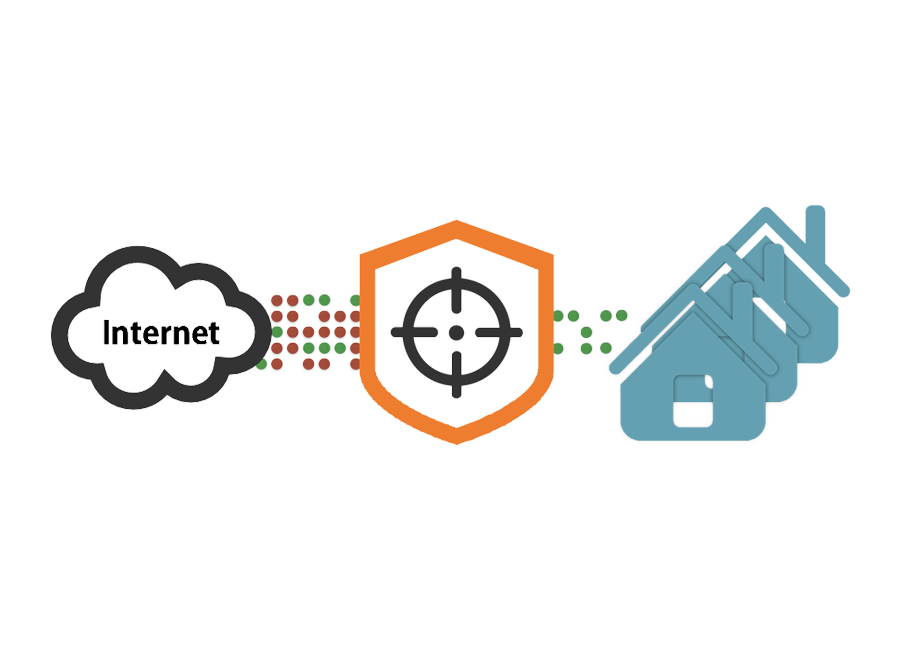
Multi-Tenancy Support for Heterogeneous Networks
When deployed in heterogeneous networks, nScrub multi-tenancy support can be used to define multiple mitigation profiles active concurrently on the same instance, by defining multiple destinations. How this works:
- Ingress traffic is split towards several virtual mitigators, based on the destination IP address, this way it is possible to specify traffic enforcement policies per destination subnet
- Each virtual mitigator is bound to traffic enforcement profiles: default, white, black, gray. Each profile contains a traffic enforcement configuration (e.g. SYN check=yes, ICMP Drop=No) and applies to source IPs according to the lists (white/black/gray).
- Global or per-destination bypass mode is supported, to handle maintenance or exclude a target
Specifications
Tech Specs
- Linux
- Web GUI available through any HTML5-ready browser with traffic statistics and engage information
- HTTP-based RESTful API for configuring the mitigation policies
- TLS/HTTPS support
- Plugins support (C)
nScrub required 4-cores 3Ghz to mitigate 10 Gbps line-rate. Performance scale increasing the number of cores.
- Ethernet/VLAN
- IPv4/IPv6
- TCP/UDP/ICMP
- GRE
models
Choose Your Model
Did you already install the software?
Select the model. Different models unlock different features and capacity. Check the comparison table.
S/M/L/XL/XXL
- Multi-layer traffic enforcement and sessions verification
- Routing mode
- Transparent bridge mode
- Hardware bypass support
- Multi-tenancy support