Internet censorship is a global phenomenon (see Figure 1) that aims to throttle or entirely block access to certain Internet resources. National or regional governments impose Internet censorship by using sophisticated networking appliances—strategically placed at the edge of their networks at various Internet inter-connection points—capable of inspecting and discarding network packets destined to sites with restricted content. Users that try to evade censorship have traditionally relied on techniques based on “domain fronting” and VPNs. However, these censorship circumvention tools are increasingly becoming harder to deploy and do not offer strong censorship resistance guarantees since regimes that impose censorship can also block access to such technologies.
Figure 1. Internet Censorship has become a global phenomenon. Figure shows prevalence of censorship via DNS injection broken down by country as measured by the Satellite project. Source: censoredplanet.org
Refraction Networking is a new censorship circumvention technique that addresses some of the shortcomings of existing circumvention tools. Refraction Networking has evolved over the past 10 years from a series of lab prototypes (i.e., Decoy Routing, Telex, Cirripede, TapDance) to a system that concurrently serves millions of users worldwide. Rather than embracing the “cat and mouse game” that, say, VPN providers and repressive regimes are engaged with (e.g., by constantly recycling VPN endpoints to avoid blockage by censors), Refraction Networking
places stations at the network’s core (e.g., within friendly ISPs, see Figure 2). Placing these stations in the “middle of the network” deters censoring entities from imposing any kind of practical censorship since their only option is to aggressively block access to the ISPs hosting the Refraction stations. This aggressive blockage would inflict collateral damage to censors themselves since they would be essentially cutting themselves off of large portions of the Internet.
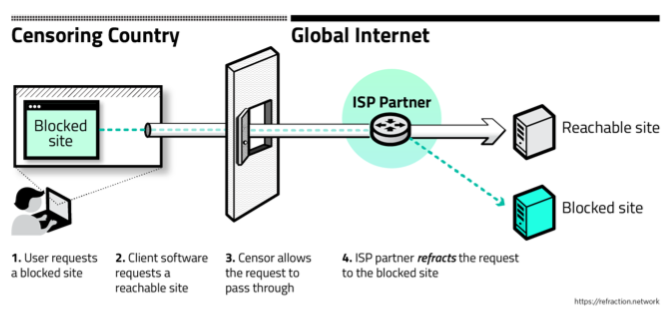
Figure 2. Refraction networking. Placing “Refraction stations” in partnering ISPs allows users to access blocked sites in a covert manner, while elevating the difficulty for censors to block Internet content.
A key component for the reliable and efficient operation of the Refraction network is the ability to monitor packets at multi-10Gbps speeds and inspect them for the steganographically encoded signal that Refraction clients use to convey their intention to connect with a “blocked” site. The Refraction network currently (passively) monitors an aggregate traffic stream that exceeds 150Gbps, and the team has relied on PF_RING ZC’s unique capabilities to deliver packets to Refraction’s monitoring engines with zero loss, even when using commodity, off-the-shelf hardware and network NICs (such as Intel Ethernet network adapters). Further, the Refraction operators utilize ntop’s zbalance_ipc to efficiently distribute the traffic load into multiple PF_RING-based worker applications that serve Refraction’s global users. The Refraction community is grateful for the support that the PF_RING team has been providing since the onset of this circumvention technology.
At the moment, the Refraction coalition consists of universities, non-profit organizations and industry partners and serves upwards of one million users worldwide. Refraction monitoring stations are currently hosted at three separate networks, including a mid-size ISP, and the team is actively seeking new partners to expand its network operations and its user population. If you are interested in joining the coalition or contributing in other ways, please reach out at team@refraction.network.
Many thanks to the members of the Refraction team who contributed to this article and for having used PF_RING to fight Internet censorship.
