NOTE: nProbe Agent features have been merged into nProbe
nProbe™ Agent
A System-Introspected Network Probe
nProbe™ Agent (formerly known as nProbe mini) is a lightweight probe that implements a low-overhead event-based monitoring, mostly based on technologies such as libebpfflow (that is based on eBPF) and Netlink.
This small agent enhances network visibility by means of system introspection while using minimal CPU and memory. It enriches classical network data such as IP addresses, bytes and packets with system-introspected processes, users, containers, orchestrators, and other performance indicators.
This makes nProbe™ Agent very effective to respond to a new series of questions that generally remain unanswered, among which:
- What is the process which is generating traffic towards a malware host? Who is the owner of this process?
- What is the latency of the communications experienced by my containers when they are communicating each other?
Features
Key features:
- Enrich network with system data such as users and processes responsible for network communications
- Export in JSON format over ZMQ and Kafka
- Out-Of-The-Box integration with ntopng
- IPv4 and IPv6 support with performance indicators
- TCP and UDP support
- Containers and orchestrators visibility (Docker, Kubernetes)
The information nProbe™ Agent is able to extract includes:
- All the TCP and UDP network communications (peers, ports, status)
- TCP counters including retransmissions, out-of-orders, and round-trip times
- Users, processes and executables behind communications
- Container IDs and names, orchestrator PODs and namespaces
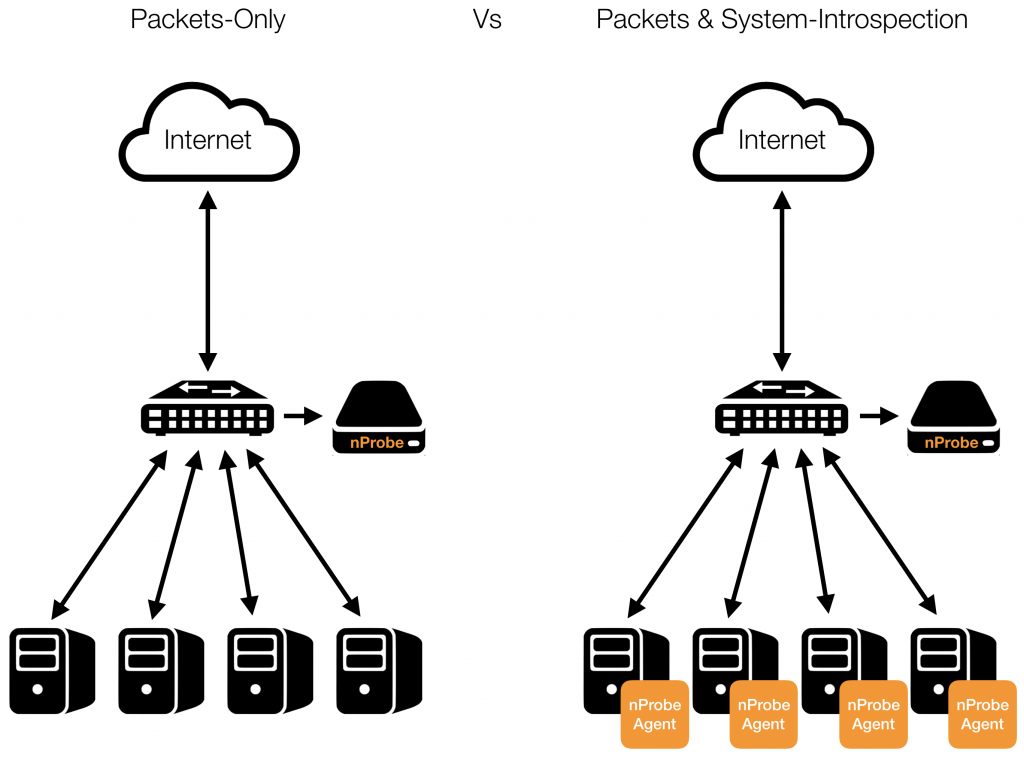
nProbe™ vs nProbe™ Agent
nProbe™ is a flow probe able to process live traffic (raw packets on a network link) or collect Netflow. nProbe™ leverages on Deep Packet Inspection (nDPI) to identify the application protocol by looking at the packet payload. nProbe™ Agent takes it a step further, providing visibility on the application that generated a given traffic, the user running the application, the real metrics the system sees (e.g. latency).
nProbe™ Agent vs ebpftoolexport
Inside libebpfflow there is a simple tool named ebpftoolexport that is featuring a subset of the features nProbe™ Agent offers. In particular it does not include NetLink support nor export over Kafka. Both tools can however be used with ntopng in order to enrich network with system introspection.
Use Cases
nProbe™ Agent provides application (and container) visibility to network flows, complementing the Deep Packet Inspection provided by nDPI. It can be used to understand system interactions while performing a network action (e.g. open a web page). To fully leverage its capabilities, it is recommended to use it in combination with the visualization and analysis tool ntopng, to learn more about this please check the documentation.
There are many use cases for this technology, some of them are listed below, just to mention a few.
Trace-Back Users and Processes Behind Network Activities
Wondering who is the user trying to download a file from a malware host? Which process is he/she running? nProbe™ Agent gives you the answer tracking all communication with clients or services running on the host and extracting all the details including the user and process using a socket.
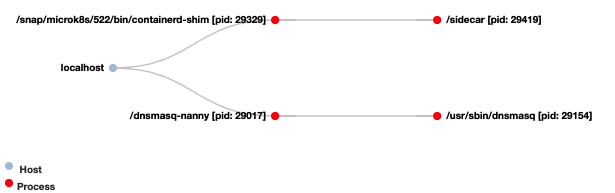
Have Visibility Into the Inter-Container Network Communications
It is common for multiple inter-communicating containers to be deployed on the same host. In this case, the traffic of their communications never reaches the wire as it always stay on the host. Hence, any attempt to monitor their traffic using mirror ports or TAPs would fail. Fortunately, nProbe™ Agent is able to detect, count and measure the network activity also when it is taking place on the host.
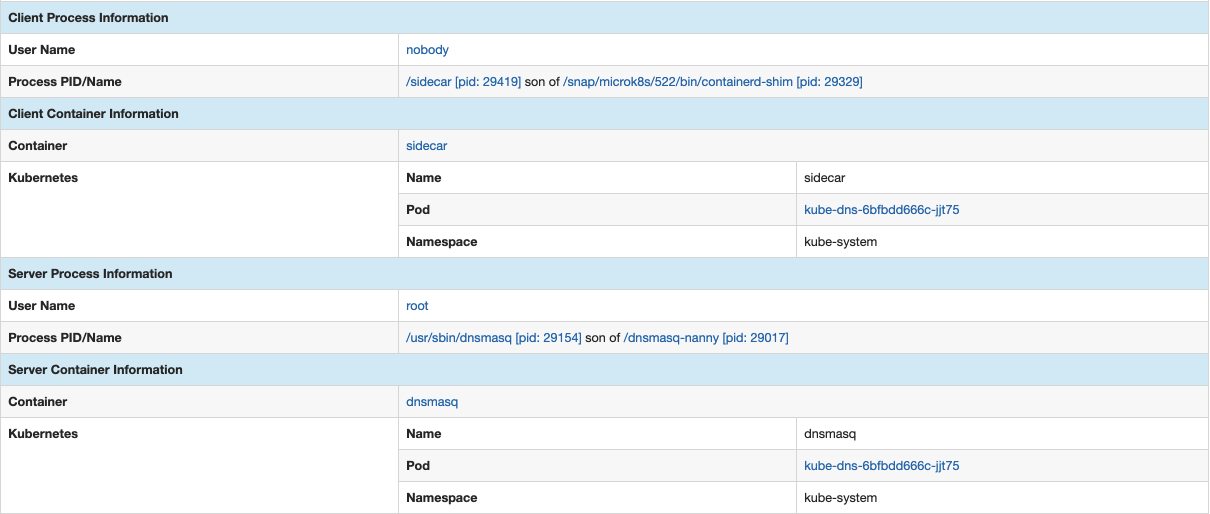
Following is a network communication as discovered by nProbe™ Agent, communication which is taking place between process /sidecar running inside container sidecar part of Kubernetes POD kube-dns-6bfbdd666c-jjt75, and process /usr/bin/dnsmasq running inside container dnsmasq part of the same Kubernetes POD.
Example of exported information:
Per-Container and Per-POD Network Activity and Performance Indicators
Curious about the performance of a given container? Interested in spotting the true bottlenecks in your OS-virtualized infrastructure? Using nProbe™ Agent you can uncover container and POD activity and performance using, for example, the measured Round-Trip times of their communications
License
nProbe™ Agent is distributed under the EULA and requires a license per system (i.e. all containers running on the same system will share the same license).
Get It
nProbe™ Agent is available in our repositories for Ubuntu 18, Ubuntu 20 and Centos 7. You can purchase online your copy of nProbe™ Agent at the ntop e-shop.