nTap
Virtual Network Tap for Hosts/Cloud/Containers/VMs
nTap is a virtual software tap that can be used in physical/virtual/cloud environments to remotely capture traffic (with respect to the monitoring location) and delivering packets to the observation point in a secure way. Packet capture is required whenever flow-based analysis tools such as nProbe/nProbe Cento are not suitable as packet-level analysis is required. The main differences between a physical tap and nTap include:
- nTap is able to deliver monitored traffic remotely (a physical tap requires a direct cable connection forcing to monitor traffic where it is generated).
- nTap delivers packets with end-to-end encryption preventing intruders from watching monitored traffic.
- nTap can apply packet filtering on monitored traffic (physical taps are unable to do this: more expensive packet brokers provide this feature).
- nTap can be used in containers and virtual machines as well highly dynamic environments such as Kubernetes (a physical tap can be used only on a physical network).
nTap is based on two components:
- nTap remote it is installed on the remote device for which need to monitor traffic.
- nTap collector receives encrypted packets sent by nTap remote, decrypts them, and push them on a virtual ethernet interface where you can attach applications such as Wireshark, tcpdump, Suricata or Snort.
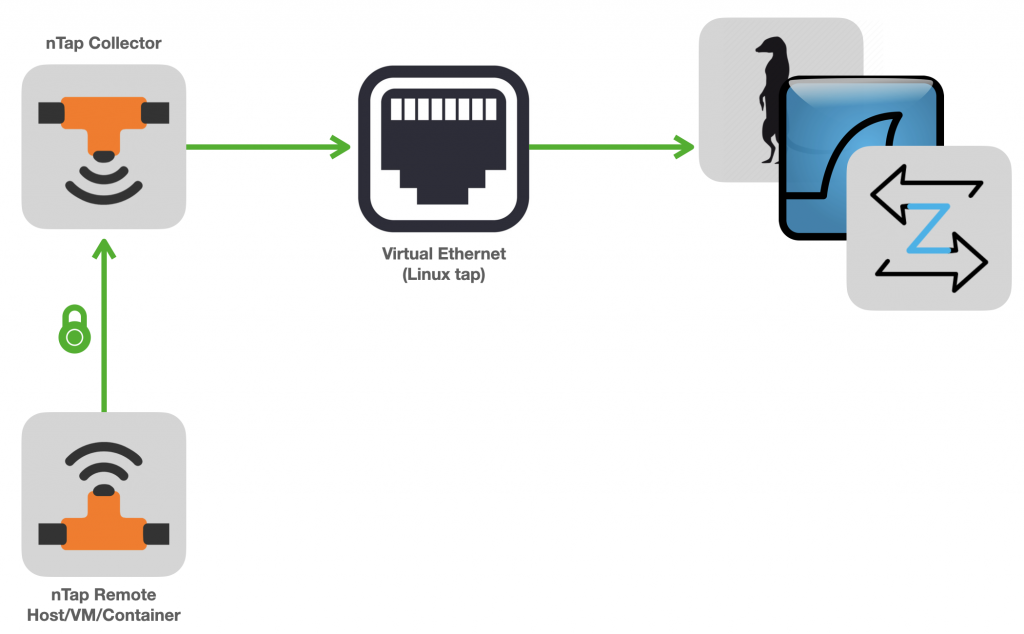
Optionally the nTap collector can also send packets to Open vSwitch for maximum flexibility.
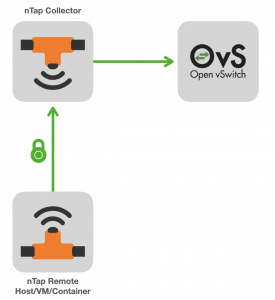
ntop applications such as nProbe (Enterprise M/L) and ntopng (Enterprise L), embed the nTap collector so that you can directly connect (one or more) nTap remote with nProbe/ntopng without the need to use the nTap collector.

Containers, Kubernetes, and Virtual Machines
nTap can be used inside containers and VMs. Typically the tap component is deployed on remote hosts/containers whose IP address can be dynamic. Instead the collector application needs to be active on a host with a static IP address as it needs to receive packets sent by the tap. No license needs to be installed on the host where the tap application runs.
Security and Performance
Contrary to many other commercial virtual tap applications, nTap delivers packets over encrypted channels over UDP. The communication is always unidirectional from the tap to the collector/ntopng/nProbe with no return channel communication: this is a key requirement in order to run nTap on a high-secure network that does not allow a return channel (note that a TCP connection is bi-directional as some packets such as ACK, need to be sent back).
The end-to-end encryption uses state-of-the-art symmetrical encryption that takes advantage (when available) of AVX instructions for maximum performance. nTap adds a micro-layer in addition to the original packet where some metadata (eg. packet capture time and length), whereas encryption does not enlarge the original packet size to be transmitted.
Documentation
The nTap user’s guide is available at this page.
License
The principle is that nTap does not need a commercial license when used with ntopng and nProbe. This is possible as ntopng Enterprise L and nprobe Enterprise M/L include native code support. In short:
- The remote tap application never needs a license. This allows you to deploy it in highly dynamic environments such as containers and VMs.
- The collector application requires a license, and it needs to be used with applications except ntopng Enterprise L and nprobe Enterprise M/L.
You can buy nTap licenses on the ntop shop if you plan to use nTap with non-ntop applications.
Note that you can use multiple remote taps sending traffic to the same nTap collector or nProbe/ntopng applications.
Operating Systems
![]()
![]()
![]()
![]()
Get It
nTap packages are available at packages.ntop.org.
