nProbe 1.0 was introduced in 2002. After 20 years we are glad to introduce nProbe 10 that introduces several new features and improvements:
- Agent mode for process monitoring on Linux (eBPF) and Windows
- Implemented timeseries support for nProbe self-monitoring and sFlow-based counter timeseries
- Conversion of Amazon AWS VPC files into flows
- Export of flows towards Google Pub/Sub
- Improved collection of proprietary flows, including Nokia and Calix
- Support for collecting flows from syslog
Agent Mode
When nProbe in deployed on a host, it is possible to use the new –agent-mode command line (available on Windows and Linux systems with eBPF support). You can start nProbe and ntopng as follows
-
nprobe -i eno1 --zmq tcp://127.0.0.1:1234 --agent-mode
-
ntopng -i tcp://127.0.0.1:1234
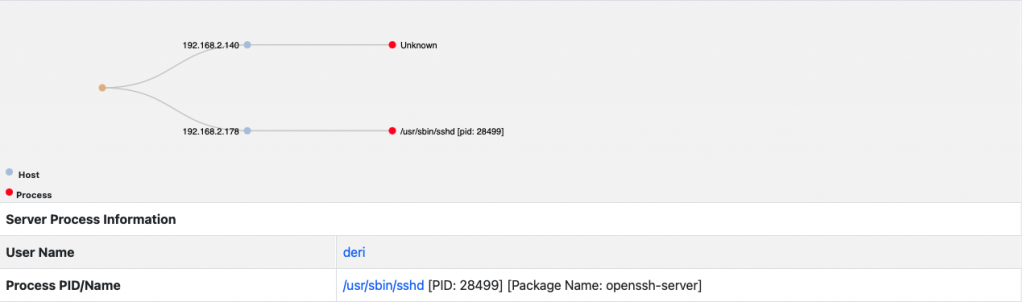
In this configuration nProbe will enrich flow information with process, user and package (Linux only) information as shown in the picture below.
Furthermore it is possible to start nProbe in process learning mode for keeping track of used processes. Example:
--process-learning <sec>:<0|1> | Process learning duration <seconds>.
| 0=means continue learning, 1=restart learning at nprobe start
For instance you can start nProbe with
-
nprobe -i eno1 --zmq tcp://127.0.0.1:1234 --agent-mode --process-learning 3600:0
for learning process started for one hour. Processes that are not part of a package or not know during learning are marked as suspicious and nProbe will return a FLOW_VERDICT information element set to drop. This is the first step towards a host-based EDR.
Timeseries
nProbe can now generated InfluxDB-compatible timeseries for the self monitoring (-b 1) and for converting sFlow-collected interface counters. You can read more about this on this blog post where we also describe how we support the timeseries generation of Calix devices.
Cloud Support
nProbe started to support cloud-based services:
- Process Amazon VPC logs and turn them into flows
- Export flows towards Google cloud for those who need to store flows on the cloud.
Collection of Proprietary Flows
In this release we have improved support of proprietary flows via custom flow definition files. In particular we have speedup proprietary fields collection and reduced memory used. Furthermore Nokia NAT/AAA correlation via proprietary flows is now fully supported.
Syslog Flow Collection
nProbe now supports syslog (UDP and TCP) flow collection via a new CLI parameter
[--syslog-flow-format] <fmt>:<port> | Parse incoming flows sent to syslog port <port>
| --syslog-flow-format 1:514 [collect on UDP:514]
| --syslog-flow-format 1:TCP/514
Currently we handle out of the box Fortinet flow syslog that can be collected and re-exported as standard flows.
This said the list of changes is very long and we invite you to have a look at the whole nProbe changelog.
Enjoy !
