Since v5 ntopng has the ability to detect periodic activities, i.e. activities that are repeated periodically at a given pace (note that each activity can have a different frequency, and ntopng is able to detect them). Periodic activities are not bad per se (e.g. an email application fetches new messages every 5 minutes) but it can be a good indicator whenever periodicity is reported in alerts.
For instance looking at the alerts below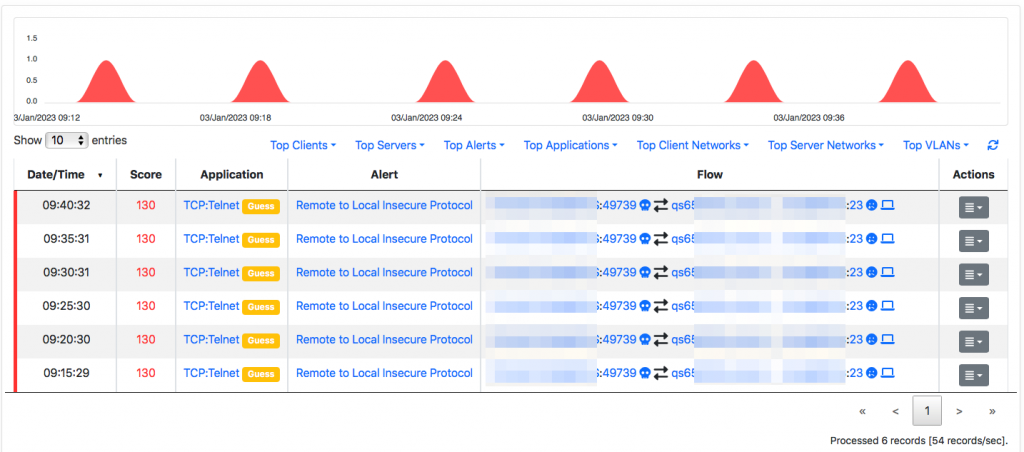 you can see that a client is making periodic requests to the same server
you can see that a client is making periodic requests to the same server
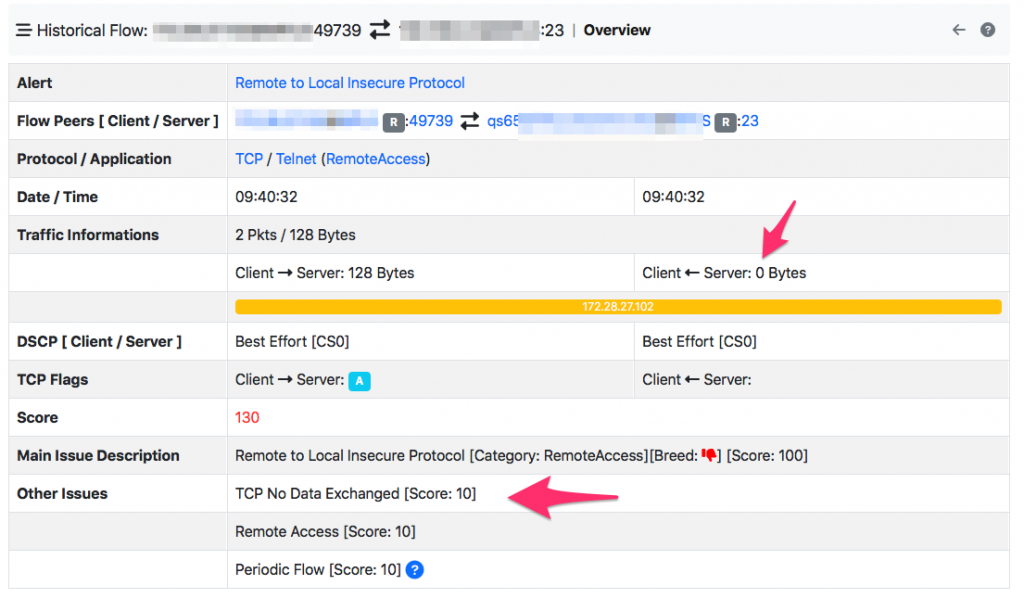
Looking at the flow, you can see that these are probing attempts as there is no response from the server side. This alert needs to be carefully analysed by security/network analysts to see if the problem is:
- a security issue (the client is using an insecure protocol to attempt server access) or a network problem (e.g. the firewall prevents legitimate activities.
- or the telnet server is down and it needs to be restored).
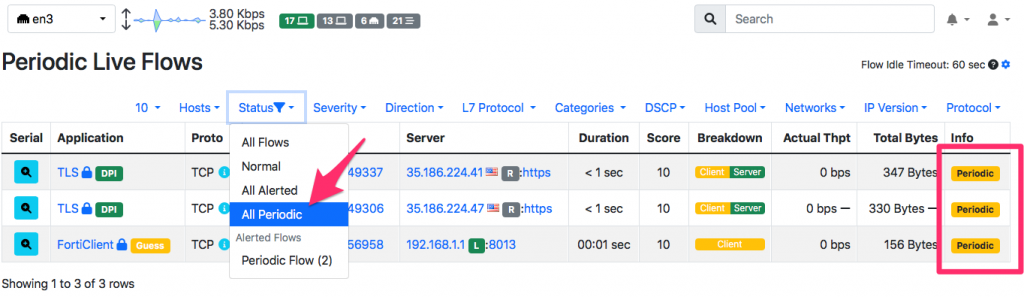
ntopng allows you to identity periodic flows not only using the periodicity map, but also filtering them in live flows view
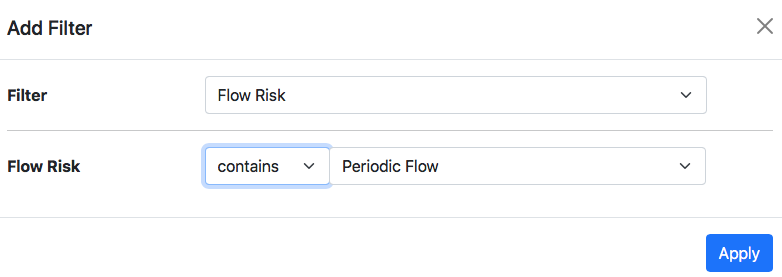
It is also possible to filter them in historical flows and alerts using the filter below (please use the “contains” operator as periodic flows can also have other issues as the alerts reported below in this page).
In conclusion: periodic activities aren’t necessarily bad, but they indicate that there is a repeating task happening overtime. A periodic alert is definitively more interesting, and it needs to be analysed to see if it indicates a failed activity that is periodically repeated, or more subtle probing attempts that instead need to be processed differently. In this analysis ntopng can definitively help you to answer the above questions.
Enjoy !