ntopng has been traditionally used to passively monitoring network traffic. However as years ago IDS (Intrusion Detection System) became mature products and eventually became IPS (Intrusion Prevention System), it was time to add inline traffic capabilities in ntopng. This post gives you s sneak preview of this new feature (still under development) that will be included in the upcoming ntopng release. The idea is to combine network traffic monitoring with traffic enforcement so that you can use ntopng not just for monitoring your users (or your children if you are on a home network) but also for making sure they don’t misuse network access with per-host/network protocol policies.
The video below shows how nDPI can be used within ntopng to enforce a specific traffic policy (in the video how to drop Skype traffic for a specific host).
[youtube=https://www.youtube.com/watch?v=NT5WHWUBQN4&w=640&VQ=HD720]
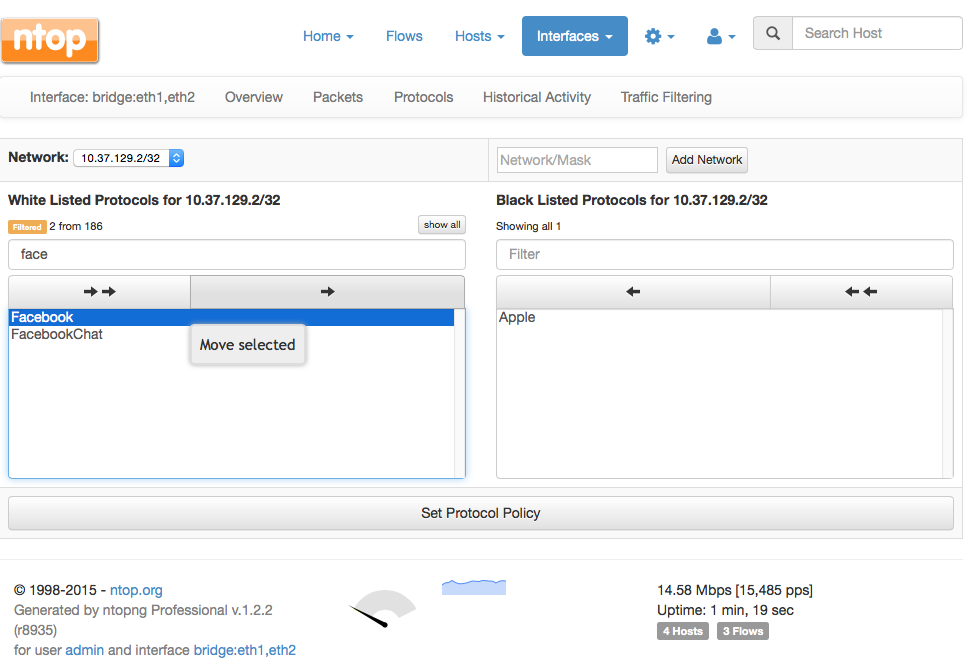
In ntopng you now have the ability to specify an interface whose name is bridge:ethX,ethY (example “bridge:eth1,eth2”) that means ntopng will bridge the traffic from the two interfaces and make sure only the allowed traffic can flow across the interfaces. When using the bridge interface, ntopng shows you in the host view the list of blacklisted protocols for a given host (note that blacklist can be specified not just per-host, but also per-network or as a global policy for everyone).
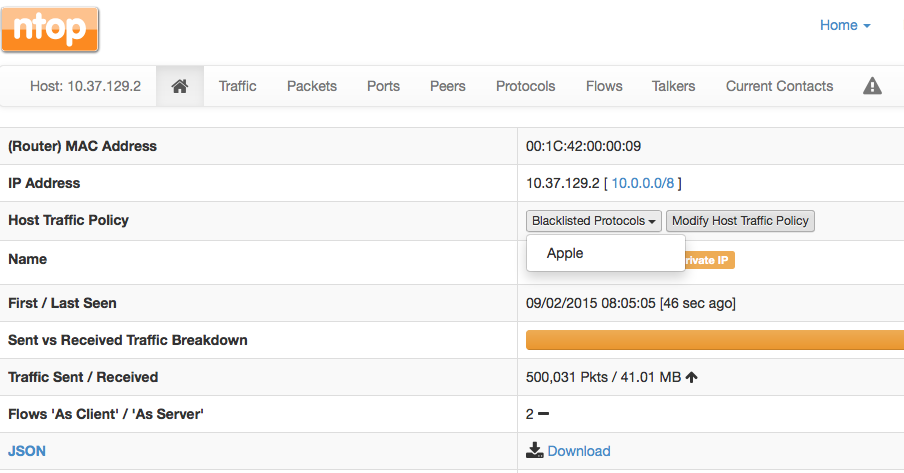
Clicking on the “Modify Host Traffic Policy” button the form below is displayed. Here network administrators can move the supported nDPI protocols (over 170 to date and include popular protocols such as Skype, WhatsApp or YouTube) from the two lists: whitelist means that the protocol can flow, blacklist means that ntopng will drop the protocol traffic.
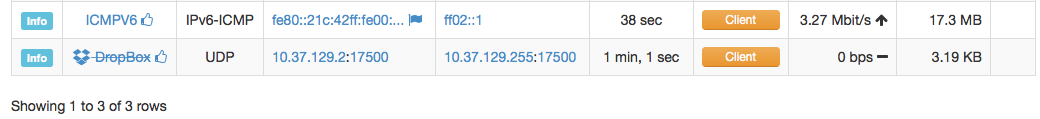
If you look at the list of flows, unwanted traffic is represented with a strikethrough style (in the example below the DropBox traffic is dropped) whereas legitimate traffic is reported as usual.
This feature is implemented on top of PF_RING ZC on Linux or over pcap for non-Linux hosts (Windows and OS X for instance). This tool is designed to run non fast multicore systems as well on low-end devices such as Raspberry Pi/BeagleBoard or Ubiquity routers. Leveraging on PF_RING ZC, ntopng can operate at line rate at 1 and 10 Gbit. In the latter case it is necessary to enable RSS in the NIC (use ethtool to instruct the NIC to hash traffic based on host IPs) and open several bridge interfaces in ntopng so that it can process the various interface queues in parallel.
As previously stated this feature will be included in the next ntopng release. While the code is working reliably, we need to further polish the configuration of policies and perhaps introduce extra features such as per-host/traffic bandwidth enforcement (i.e. host X cannot send more than Y pps/Mbps). This said it won’t take too long before we release it.
Stay tuned!